Endpoint detection and response (EDR) security is emerging as one of the most useful forms of network security in today’s landscape. Before diving into the specifics of how EDR actually works, it’s important to get a primer on the concepts and reasoning behind EDR. Once both of those have been established, we can look deeper at why EDR specifically is so important for modern enterprise network security.
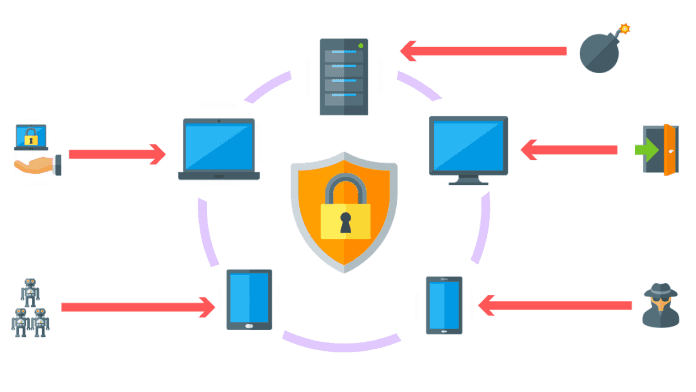
At the most basic level, EDR aims to provide continuous monitoring of endpoints. These are essentially any and all devices connecting to enterprise networks, including smartphones, laptops, Internet-of-Things (IoT) sensors, tablets, and others. As more and more endpoints—especially those that aren’t internally provided and vetted, such as personal devices—connect to networks, it creates additional challenges, as there are more attack surfaces ripe for exploitation.
You probably know there are various forms of enterprise cybersecurity tools that monitor network traffic for suspicious activity, or investigate packet-level data for abnormalities. Antivirus software, firewalls, and other network security technologies work together to uncover threats in traffic. EDR is different because it focuses on endpoints themselves. It will become clear as to why this keeps becoming an increasingly important defense approach for enterprise network security. With that, let’s dig into how EDR works.
How Does EDR Work?
So, you understand that EDR enables better monitoring of endpoints that are connecting to enterprise networks. But how exactly does EDR accomplish this? There are a few elements to EDR that allow it to provide organizations better security.
The process must begin with ongoing monitoring of all endpoints connecting to the enterprise network. This needs to be done in real-time to ensure any strange activity can be spotted and investigated before threats can grow into a full-blown breach. A good EDR solution will analyze the behavior of endpoints and be able to send out instant, automated alerts to relevant parties when investigation or triage might be necessary.
It’s important to note that not all devices that connect to an enterprise network are going to be there all the time. For devices that periodically come and go, it’s essential endpoint detection and response security can keep running logs of activity for each individual device. Having a log of all endpoint activity allows for more comprehensive and accurate analysis of device behavior, which can lead to spotting issues sooner.
Beyond having continuous monitoring and real-time incident response, it’s wise to opt for an EDR that offers managed services. You want to have the best players on your team when dealing with an active threat. Service-based EDR solutions, such as what’s offered by Open Systems, bring their squad of expert engineers onto your security force. Having industry-leading expertise ready to step in to stop attacks on enterprise networks can help stakeholders sleep better at night.
Why Is EDR Important for Enterprise Network Security?
As already mentioned, EDR is an important consideration for enterprises today because more and more devices are connecting to networks. The number of Internet-of-Things (IoT) devices is currently in the middle of an exponential growth phase—taking it from under a billion total in 2010, to what’s predicted to be over 30 billion by 2025. All of these devices will create new attack surfaces, which need to be addressed and secured by organizations.
Furthermore, the combination of bring-your-own-device policies, combined with the shift to remote work, which was accelerated by COVID-19, creates more security issues for enterprises. There’s no way for IT departments to reliably enforce what people are doing with their personal devices, which are then connecting to organizational networks. Creating stronger endpoint security can help keep lurking threats from compromising critical data.
EDR is a useful variety of network security that has a place in every organization’s defense suite. Finding an EDR that has a combination of powerful endpoint monitoring and analysis, as well as the best security experts on-call, can greatly improve the chances of stopping a threat before it gets out of hand.